The Secure AI Checklist.
How to use AI at work without leaking data, creating unmanaged risk, or letting employees freestyle with sensitive information.
- What employees should and shouldn't enter into AI tools
- Vendor review questions before you sign
- Access control basics — SSO, MFA, revocation
- Where human approval is non-negotiable
- Governance roles and an incident response path
- Your first safe rollout, sized to a single team
Get the Secure AI Checklist
Tell us a little about your environment and we'll tailor the next step to your industry.
A defensible AI policy,
in one document.
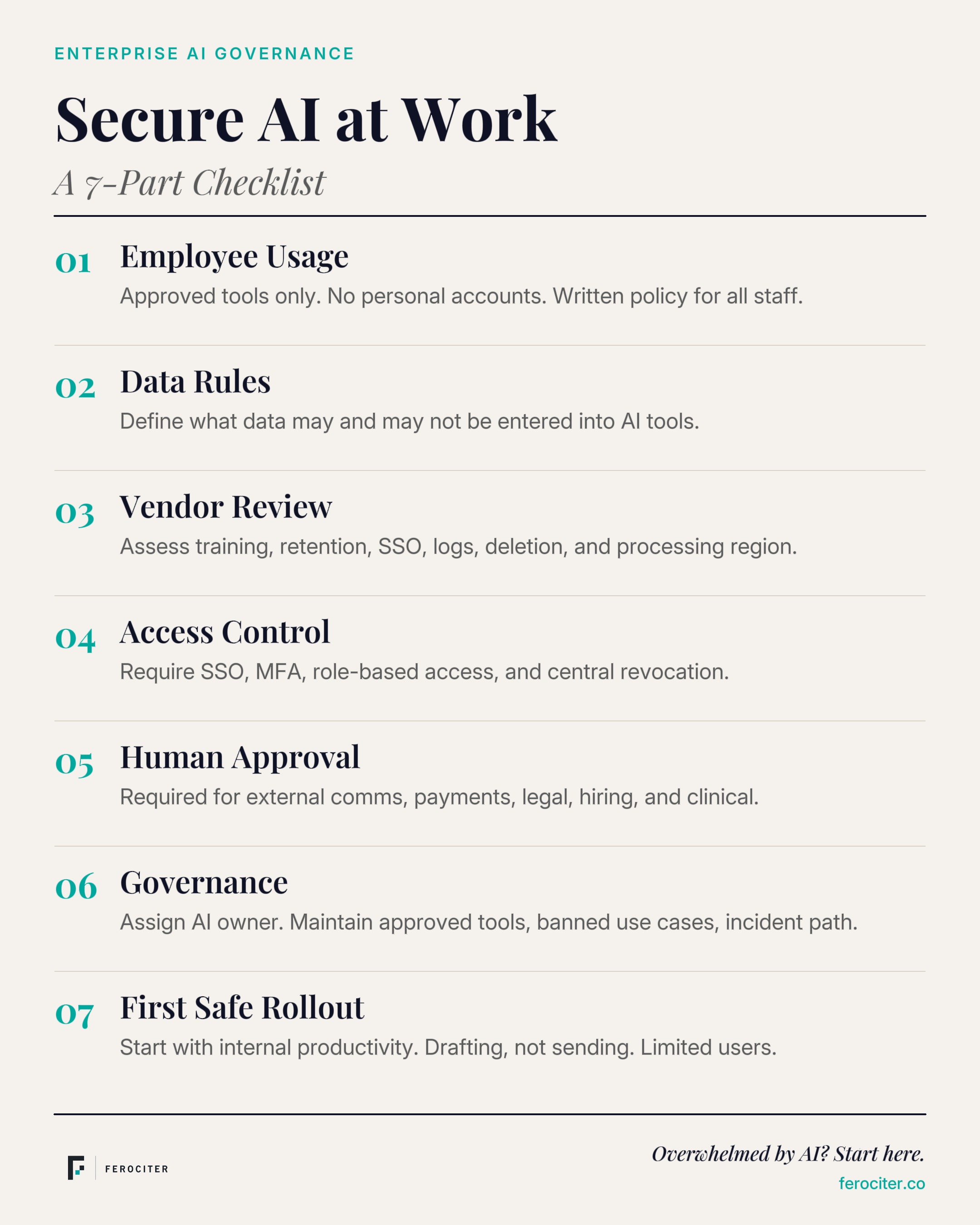
Employee usage
Approved tools, no personal accounts, written usage policy.
Data rules
Define what data may and may not be entered into AI tools.
Vendor review
Training, retention, SSO, logs, deletion, processing region.
Access control
SSO, MFA, role-based access, central revocation, key hygiene.
Human approval
Required for external comms, payments, legal, hiring, clinical.
Governance
AI owner, approved tools, banned use cases, incident path.
First safe rollout
Internal productivity. Drafting, not sending. Limited users.
Secure AI at work.
At a glance.
Pin this to a wall. Send it to your CISO. Use it as the table of contents for your first AI policy meeting.
We write AI policies that
your security team will sign off on.
Strategy, training, governance, and custom implementation. The roadmap call is where it starts.